![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
113 Cards in this Set
- Front
- Back
|
3 main points of ML definition
|
The conversion or transfer of property, knowing it is
derived from a criminal offense, for the purpose of concealing or disguising its illicit origin The concealment or disguising of the true nature, of property knowing that it is derived from a criminal offense The acquisition knowing at the time of its receipt that it was derived from a criminal offense or from participation in a crime. |
|
|
willful blindness
|
Courts define
it as the “deliberate avoidance of knowledge of the facts” or “purposeful indifference.” |
|
|
October 2001 the FATF expanded _______
|
its mandate to cover the financing of terrorism.Terrorist funds are sometimes not derived through illegal means.
|
|
|
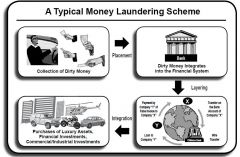
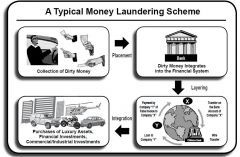
3 stages of Money Laundering Cycle
|
Step One: Placement
Step Two: Layering Step Three: Integration |
|
|
Step One: Placement
|
During this initial phase, the money launderer
introduces his illegal proceeds into the financial system. Often, this is accomplished by placing it into circulation through financial institutions, casinos, shops, bureaux de change and other businesses, both domestic and international. |
|
|
Step Two: Layering
|
q Wire transfers of deposited cash from one
account to another q Converting deposited cash into monetary instruments (e.g. traveler’s checks) q Reselling high-value goods and monetary instruments q Investing in real estate and legitimate businesses. q Use of shell banks, which are typically registered in offshore havens, and wire transfers. |
|
|
Step Three: Integration
|
Supplying apparent
legitimacy to illicit wealth by the re-entry into the economy of what appear to be normal business funds. The third and final stage in the money laundering process, this stage entails placing laundered proceeds back into the economy to create the perception of legitimacy. By the integration stage, it is exceedingly difficult to distinguish legal and illegal wealth. The launderer might choose to invest the funds in real estate, luxury assets or business ventures. |
|
|
|
|
|
Some of the effects of money laundering and terrorist financing
are: |
n Increased Crime and Corruption:
n Undermining the Legitimate Private Sector: n Weakening Financial Institutions: |
|
|
Increased Crime and Corruption:
|
Typically, havens for money laundering and
terrorist financing have: Limited number of predicate crimes for money laundering, A restricted definition of institutions covered by money laundering laws and regulations, Little enforcement of the laws, weak penalties, provisions that make it difficult to confiscate or freeze assets related to money laundering. If money laundering is prevalent, there |
|
|
Undermining the Legitimate Private Sector:
|
front companies have a competitive advantage over legitimate firms that draw capital funds from financial markets. It also provides a vehicle for evading taxation, thus depriving the country of revenue.
|
|
|
Weakening Financial Institutions:
|
Financial institutions that rely on the proceeds of crime
have additional challenges in adequately managing their assets, liabilities and operations. The adverse consequences of money laundering are generally described as reputational, operational, legal and concentration risks. |
|
|
consequences of money laundering are generally
described as reputational, operational, legal and concentration risks. |
Loss of profitable business;
Liquidity problems through withdrawal of funds; Termination of correspondent banking facilities; Investigation costs and fines; Asset seizures; Loan losses; Reduced stock value of financial institutions. |
|
|
Reputational risk
|
the potential that
adverse publicity regarding a bank’s business practices and associations, whether accurate or not, will cause a loss of public confidence in the integrity of the institution. |
|
|
Operational risk
|
the potential for loss resulting from
inadequate or failed internal processes, people and systems or external events. |
|
|
Legal risk
|
the potential for lawsuits, adverse
judgments, unenforceable contracts, fines and penalties generating losses, increased expenses for an institution, or even closure of such an institution. |
|
|
Some indicators of money laundering using electronic transfers of
funds are: |
Any transfer/deposit made from high risk location that is not in line with customer pattern or any apparent reason
|
|
|
Correspondent banking
|
the provision of banking services by one
bank (the ‘correspondent bank’) to another bank (the ‘respondent bank’). By establishing multiple correspondent relationships globally, banks can undertake international financial transactions for themselves and for their customers in jurisdictions where they have no physical presence. |
|
|
Correspondent banking is vulnerable to money laundering for two
main reasons: |
1. financial institution carries out financial transactions on behalf of customers from another institution.
2. a correspondent relationship astronomical amounts of money can come from many directions. |
|
|
Additional risks incurred by the correspondent bank include:
|
While the correspondent bank may be able to learn
what laws govern the respondent bank, determining the degree and effectiveness of the supervisory regime to which the respondent is subject is much more difficult. Some banks offering correspondent facilities may not ask their respondents about the extent to which they offer such facilities to other institutions (“Nesting”). This adds another layer and means the correspondent bank |
|
|
payablethrough
accounts (PTAs). |
the foreign bank’s local
customers are permitted to conduct their own transactions — including wire transfers, deposits withdrawals and maintain checking accounts — through the foreign bank’s U.S. correspondent account. |
|
|
Elements of a PTA relationship that can threaten the domestic
bank’s money laundering defenses include: |
PTAs with foreign institutions licensed in offshore
financial services sectors with weak or absent bank supervision and weak licensing laws, PTA arrangements where the domestic bank regards the foreign bank as its sole customer and fails to apply its Know Your Customer policies and procedures to the customers of the foreign bank, PTA arrangements in which sub-account holders have currency deposit and withdrawal privileges, PTAs used in conjunction with a subsidiary, representative or other domestic office of the foreign bank, which may enable the foreign bank to offer the same services as a branch without being subject to supervision. |
|
|
Concentration accounts
|
internal accounts established to
facilitate the processing and settlement of multiple or individual customer transactions within the bank, usually on the same day. frequently used to facilitate transactions for private banking, trust and custody accounts, funds transfers and international affiliates. |
|
|
Money laundering risk can arise in concentration accounts ____
|
if
the customer-identifying information, such as name, transaction amount and account number, is separated from the financial transaction. If separation occurs, the audit trail is lost, and accounts may be misused or administered improperly. Banks that use concentration accounts should implement adequate policies, procedures and processes covering operation and recordkeeping for these accounts. |
|
|
anti-money laundering practices for concentration accounts
|
Requiring dual signatures on general ledger tickets.
NO customer access to concentration accounts. customer transactions in the customer’s account statements. Prohibiting customer’s knowledge of concentration accounts appropriate transaction and customer identifying information. Frequent reconciling of the accounts by an individual who is independent from the transactions. Establishing timely discrepancy resolution process. Identifying recurring customer names. |
|
|
These factors may contribute to private banking’s vulnerability to
money laundering: |
Perceived high profitability and intense competition
The high level of confidentiality associated with private banking The close relationships of trust developed between relationship managers and their clients. Commission-based compensation for relationship managers |
|
|
Private Banking
|
Private banking provides highly personalized and confidential
products and services to well-heeled clients at fees that are often based on “assets under management.” Private banking often operates semi-autonomously from other parts of a bank and caters to wealthy customers who seek confidentiality and personalized service. fiercely competitive |
|
|
Smurfing/Structuring
|
Designing a transaction to evade triggering a reporting or
recordkeeping requirement. probably the most commonly known ML method. |
|
|
|
|
|
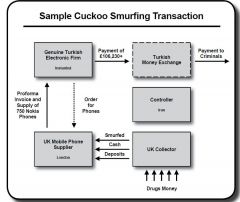
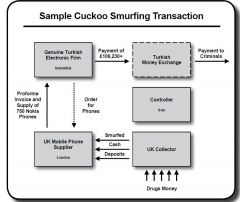
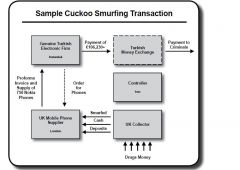
cuckoo smurfing
|
criminal funds are transferred through
the accounts of unwitting persons who are expecting genuine funds or payments from overseas. |
|
|
some bank managers
in Pakistan sell to remittance system operators genuine personal electronic transfers to be performed on behalf of legitimate customers. |
|
|
According to the FATF, the following should be kept in mind when
dealing with possible cuckoo smurfing activity: |
The existence of these deposits is not necessarily
grounds to reconsider the relationship with a customer; It could be the indicator of laundering, therefore should be subject to suspicious activity reporting; Law enforcement will need information on the depositor, so banks should seek to identify cash deposits made by third parties and retain surveillance footage. |
|
|
Version 1 credit unions
|
only offers basic savings and loan products
|
|
|
Version 2 credit unions
|
broader range of financial services which pose a higher risk since they tend to contain a larger
clientele and offer potential criminals a larger range of possible ways to conceal their illicit funds. |
|
|
Version 1 credit unions
|
only offers basic savings and loan products
|
|
|
Version 2 credit unions
|
broader range of financial services which pose a higher risk since they tend to contain a larger
clientele and offer potential criminals a larger range of possible ways to conceal their illicit funds. |
|
|
JMLSG
|
United Kingdom’s Joint Money Laundering Steering Group
|
|
|
JMLSG's 5 additional points for credit unions to have to combat ML risk
|
1. paying close attention to clientele, products, and the
institution’s location. 2. outlines for managing and controlling the assessed risks. 3. Methods for monitoring and improving internal operations. 4. Documentation of steps taken to prevent risk and the reasons behind those decisions. 5. Instructions on record-keeping procedures. |
|
|
The credit card industry includes:
|
Credit card associations, such as American Express,
MasterCard and VISA, Issuing banks, which solicit potential customers and issue the credit cards; Acquiring banks, which process transactions for merchants who accept credit cards; And third-party processors, which contract with issuing or acquiring banks to provide transaction processing and other credit card–related services for the banks. |
|
|
which stage of ML is more likely in credit card ML?
|
Credit card accounts are not likely to be used in the initial
placement stage of money laundering, because the industry generally restricts cash payments. They are more likely to be used in the layering or integration stages. |
|
|
4 different operations of remittance services
|
Funds transfer companies possessing separate
networks (like Western Union and Money Gram); Money transfer systems connected with clandestine banks (underground banking); Money transfers by way of the collection accounts of foreign banks International money orders. |
|
|
2 ways remittance services can foster ML
|
1. packages containing large cash sums and even drugs
anonymously. 2. Another technique commonly used by money remitters and currency exchanges is for the broker to make the funds available to the criminal organization at the destination country in the local currency. |
|
|
what is an annuity?
|
An annuity is an investment that provides a defined
series of payments in the future in exchange for an up-front sum of money. |
|
|
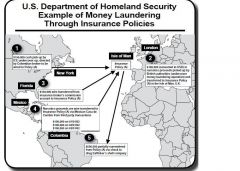
Most significant laundering and terrorist financing risks in the
insurance industry are found in____ |
life insurance and annuities
products. |
|
|
Vulnerabilities in the insurance sector include (4 points):
|
Lack of oversight/controls on intermediaries:
Lack of training: Sales-driven objectives: Lack of knowledge: |
|
|
Lack of oversight/controls on intermediaries:
|
Insurance brokers have a great deal of control
and freedom regarding policies. They often maintain pre-signed payment instructions for policy withdrawals to enable clients to make such withdrawals with a telephone call. Brokers sometimes pay insurance premiums from their own accounts; presumably they are reimbursed by the client in cash. |
|
|
Lack of training:
|
Insurance brokers often have no or
little training in anti-money laundering issues and can be used to place cash funds into various financial institutions. Some insurance companies fail to identify indicators of money laundering, such as payments for insurance products by unrelated third parties or use of consecutively numbered checks or money orders. |
|
|
Sales-driven objectives:
|
The focus of brokers is on
selling the insurance products, and thus they often overlook signs of money laundering, such as presigned forms, lack of explanation for wealth or unusual methods for paying insurance premiums. |
|
|
Lack of knowledge:
|
In addition to a lack of knowledge
of the client and the source of his or her funds, insurers often have little knowledge of the complex pyramid of sub-brokers employed by their agents. |
|
|
Examples of how money can be laundered through the insurance
industry include: |
The customer can over-fund the policy, moving funds into and out of the
policy for the cost of early withdrawal penalties. Purchase and redemption of single premium insurance bonds are key laundering vehicles. The bonds can be purchased from insurance companies and then redeemed prior to their full term at a discount. Early redemption: One indicator of possible money laundering is when a potential policyholder is more interested in cancellation terms of a policy than the benefits of the policy. |
|
|
When a company assesses laundering and terrorist financing risks,
it must consider whether it permits customers to (3 points): |
Use cash or cash equivalents to purchase insurance
products Purchase an insurance product with a single premium or lump-sum payment Borrow money against an insurance product’s value. |
|
|
|
|
|
6 Aspects of the securities
field that increase its exposure to laundering are: |
Its international nature
Fast-paced transactions, often at the click of a mouse The easy conversion of holdings to cash without significant loss of principal The routine use of wire transfers from, to or through multiple jurisdictions The competitive, commission-driven environment, which, like private banking, provides ample incentive to disregard the source of client funds The practice of brokerage firms maintaining securities accounts as nominees or trustees, thus permitting concealment of the identities of the true beneficiaries |
|
|
Money laundering through casinos occurs generally in the
placement stage, i.e. converting the funds to be laundered from cash to checks. How? |
A launderer can buy chips with cash generated
by a crime and then request repayment by check drawn on the casino’s account. Often, rather than requesting repayment by check in the casino where the chips were purchased with cash, the gambler says that he will be traveling to another country in which the casino chain has an establishment, asks for his credit to be made available there and withdraws it in the form of a check in the other jurisdiction. |
|
|
more reliable ML technique connected with horse-racing and gaming
|
when the person will
actually gamble the money to be laundered, but in such a way as to be reasonably sure of ultimately more or less recovering his stake in the form of checks issued by the gambling or betting agency and corresponding to perfectly verifiable winnings from gaming. |
|
|
The following transactions of High-Value Items
(Precious Metals, Jewelry, Art, etc.) are also vulnerable, and require additional attention: |
Payments or returns to persons other than the owner
Precious metal pool accounts — These are maintained by a small number of large and sophisticated precious metal companies, and have world-wide scope. They receive and hold precious metal credits for a customer, and can be drawn on by that customer for return of that precious metal, or for sale and return of monetary proceeds, or for delivery of precious metal to another person. |
|
|
Art and antiques dealers and auctioneers should follow these tips
to lessen their money laundering risks: |
Require all art vendors to provide names and
addresses. Verify the identities and addresses of new vendors and customers. If there is reason to believe an item might be stolen, immediately contact the Art Loss Register (www. artloss.com), the world’s largest private database of stolen art. Look critically when a customer asks to pay in cash. Avoid accepting cash payments unless there is a strong and reputable reason to do so. Be aware of money laundering regulations. Appoint a senior staff member to whom employees can report suspicious activities. |
|
|
4 Ways money laundering can occur in travel agencies include:
|
Purchasing an expensive airline ticket for another
person who then asks for a refund Structuring outgoing wire transfers in small amounts to avoid recordkeeping requirements, especially those from foreign countries and unusually large amounts Sending a tour group to a country and making an offsetting payment in a foreign entity’s U.S. or other account while instructing the accountholder to cover the cost of the group’s trip Arranging complex payment or invoicing for customers, thereby structuring cash payments to avoid currency reports. |
|
|
4 Laundering risks and ways laundering can occur through vehicle
sellers include: |
Structuring cash deposits below the reporting
threshold, or purchasing vehicles with structured checks and money orders Trading in vehicles for other ones and conducting successive transactions of buying and selling new and used vehicles to produce complex transaction layers Arranging complex payment or invoicing for customers, thereby structuring cash payments to avoid currency reports Accepting third-party payments, particularly from jurisdictions with lax laundering controls. |
|
|
5 functions provided by lawyers, notaries, accountants
and other professionals are the most useful to a potential money launderer: |
Creation of corporate vehicles or other complex legal
arrangements (trusts, for example). Such constructions may serve to confuse the links between the proceeds of a crime and the perpetrator. Buying or selling property. Performing financial transactions. Financial and tax advice. Gaining introductions to financial institutions. |
|
|
Commodity futures and options accounts are vehicles that could be
used to launder illicit funds. What are they? |
Commodity:
Commodity pool: Futures/futures contract: Omnibus account: Options/options contract: |
|
|
Commodity:
|
Goods such as food, grains and
metals that are usually traded in large amounts on a commodities exchange, usually through futures contracts. |
|
|
Commodity pool:
|
Combines funds from various
members and uses them to trade in futures or options contracts. |
|
|
Futures/futures contract:
|
A contract to buy or sell a
quantity of a commodity at a future date at a set price. |
|
|
Omnibus account:
|
An account held by one futures
commission merchant (FCM) for another. Transactions of multiple account holders are combined and their identities are unknown to the holding FCM. |
|
|
Options/options contract:
|
The right, but not the
obligation, to buy or sell a set amount of something, such as a share or commodity, at a set price after a set expiration date. |
|
|
Commodity pool operator:
|
Operator or solicitor of funds
for a commodity pool, which combines funds from members and trades futures or options contracts. |
|
|
Commodity trading adviser:
|
Direct or indirect advisor
on buying and selling futures or commodity options. |
|
|
Futures commission merchant (FCM):
|
A firm or person
that solicits or accepts orders on futures contracts or commodity options and accepts funds for their execution. |
|
|
Introducing broker-dealers in commodities (IB-Cs):
|
A firm or person that solicits and accepts commodity
futures orders from customers but does not accept funds. There are two types of IB-Cs, guaranteed and independent. |
|
|
Guaranteed introducing broker:
|
An introducing brokerdealer
with an exclusive written agreement with a futures commission merchant that obligates the FCM to assume responsibility for the introducing broker’s performance. |
|
|
Investment adviser:
|
Persons who, for compensation,
provide advice on securities and investments and manage client assets. |
|
|
6 ways commodities/trading is susceptible to money
laundering. |
Withdrawal of assets through transfers to unrelated
accounts or to high-risk countries Frequent additions or withdrawals from accounts Checks drawn on, or wire transfers from, accounts of third parties with no relation to the client Clients who require custodial arrangements that allow them to remain anonymous Transfers of funds to the adviser for management followed by transfers to accounts at other institutions in a layering scheme Investing illegal proceeds for a client Movement of funds to disguise their originator. |
|
|
2 Ways to launder money in Real Estate
|
1. by way of chain
transactions in real estate to cloak the illicit source of funds (the layering phase), 2. by investment in, for example, tourist or holiday complexes that lend an appearance of legality (the integration phase). |
|
|
“reverse flip”
|
A money launderer
might find a cooperative property seller who agrees to a reported purchase price well below the actual value and then accepts the difference “under the table.” |
|
|
“loan back” money laundering method,
|
a criminal provides
an associate with a specific amount of illegitimate money. The associate then provides a “loan or mortgage” back to the trafficker for the same amount with all the necessary “loan and/or mortgage” documentation. This creates an illusion that the trafficker’s funds are legitimate. The scheme is reinforced through “legitimately” scheduled payments made on the loan by the traffickers. |
|
|
Black Market Peso Exchange (BMPE)
|
is a process by which
money in the U.S. derived from illegal activity is purchased by Colombian “peso brokers” from criminals in other countries and deposited in U.S. bank accounts that the brokers have established. |
|
|
ML in inporting/exporting
|
can move
money out of one country by simply using their illicit funds to purchase high-valued products, and then exporting them at very low prices to a colluding foreign partner, who then sells them in the open market at their true value. |
|
|
ML in inporting/exporting
|
can move
money out of one country by simply using their illicit funds to purchase high-valued products, and then exporting them at very low prices to a colluding foreign partner, who then sells them in the open market at their true value. |
|
|
ML risks with online banking
|
The nature of online banking itself, with an elimination
of face-to-face contact between customer and employee, will necessarily make it more difficult to know who is actually controlling the account The ease of access through the Internet The rapidity of electronic transactions. |
|
|
To combat cyberlaundering, the FATF suggests these 4 points:
|
Internet service providers establish log files with
traffic data that produces Internet-protocol numbers of subscribers and telephone numbers used for server connections Information collected through the servers be shared with law enforcement agencies Information collected be maintained for up to a year Internet service providers keep records, including identification information, on those who transit through their servers. |
|
|
How online banking aids ML in PLACEMENT
|
cyberspace banks have the
potential to offer highly secure, uncommonly private “placement” vehicles for money launderers. |
|
|
How online banking aids ML in LAYERING
|
Electronic mail messages, aided by
encryption and cyberspace banking transfers, will enable launderers to transfer assets around the world many times a day. |
|
|
How online banking aids ML in INTEGRATION
|
If cyberbanking permits person-to-person cash-like
transfers, with no actual cash involvement, existing currency reporting regulations may not apply. Using “super smart-card” technologies, cash could be moved around the world through ATM transactions. These smart cards promise easy retrieval of the “account” balance by using an ATM card. |
|
|
ML risks for ONLINE GAMBLING
|
For example, transactions are primarily
performed through credit cards, and the offshore location of many Internet gambling sites makes locating and prosecuting relevant parties difficult if not impossible. Furthermore, gambling transactions — the records of which might be needed as evidence — are conducted at the gambling site and are software-based; this may add to the difficulty of collecting and presenting such evidence. |
|
|
6 ML risks for Prepaid cards
|
Anonymous card holders
Anonymous funding and anonymous access to funds High value limits and no limits on the number of cards individuals can acquire Global access to cash through ATMs Offshore card issuers may not observe laws in all jurisdictions Substitute for bulk-cash smuggling |
|
|
5 Measures that might limit the vulnerability to money laundering of
new payment technologies are: |
Limiting the functions and capacity of smart cards
(including maximum value and turnover limits, as well as number of smart cards per customer); Linking new payment technology to financial institutions and bank accounts; Requiring standard record keeping procedures for these systems to enable the examination, Documentation, and seizure of relevant records by investigating authorities; and Establishing international standards for these measures. |
|
|
Shelf company:
|
A corporation that has had no activity. It has been
created and put on the “shelf”. This corporation is then later usually sold to someone who would prefer to have an existing corporation than a new one. |
|
|
Shell company/corporation:
|
A company that is incorporated that
at the time has no significant assets or operations. |
|
|
7 laundering
techniques used in conjunction with criminal controlled companies: |
Using Nominees as Owners or Directors
Layering Loans Fictitious business expenses/False invoicing Sale of the business Buying a company already owned by the criminal enterprise Paying out fictitious salaries |
|
|
Using Nominees as Owners or Directors
|
To
distance a company from its criminal connections, nominees will be used as company owners, officers and directors. Nominees will often, but not necessarily, have no criminal record. Often, companies established by lawyers will be registered in their name. |
|
|
Layering
|
In some cases, a number of companies
were established, many of them connected through a complex hierarchy of ownership. This helps to conceal criminal ownership and facilitates the transfer of illicit funds between companies, muddying any paper trail. |
|
|
Loans
|
Proceeds of crime can be laundered
by lending money between criminally-controlled companies. In one case, the Canadian report says a Toronto drug trafficker had $500,000 in a bank account in the name of a shell company. These funds were re-invested in restaurants operated by the criminal enterprise and costing $1 million. A down payment of $50,000 in legitimate money was made and properly declared. A $450,000 mortgage was then negotiated from a bank. The remaining $500,000 was “borrowed” from the bank account of the criminal enterprise’s shell company. The $500,000 was repaid with interest to avoid suspicion. |
|
|
Fictitious business expenses/False invoicing
|
The report says that once a criminal enterprise
controls corporate entities in different jurisdictions, it can employ a laundering technique known as “double invoicing.” An offshore corporation orders goods from its subsidiary in Canada, and the payment is sent in full to the bank account of the Canadian subsidiary. Both companies are owned by the criminal enterprise and the “payment” for goods is actually a repatriation of illicit money previously spirited out of the country. Moreover, if the Canadian company has been charged a high price for the goods, the books of the Canadian company show a low level of profit, which means that company will also pay less in taxes. |
|
|
Sale of the business
|
When the criminal sells the
business, he has a legitimate source or capital. The added benefit of selling a business through which illicit money circulates is that it will ostensibly exhibit significant cash flow and, as such, will be an attractive investment and realize a high selling price. |
|
|
Buying a company already owned by the criminal
enterprise |
An effective laundering technique is to
“purchase” a company already owned by the criminal enterprise. This laundering method is most frequently used to repatriate illicit money that was previously secreted in foreign tax havens. Criminal proceeds from offshore are used to buy a company that is already owned by the criminal enterprise. In this way, the launderer successfully returns a large sum of money to Canada. Often, the business will be purchased at an artificially inflated price. The difference between the artificial and the real market value is deposited in the bank account of a foreign subsidiary company in a tax haven country. A reverse situation may occur where a Canadian company is sold at an artificially low price. |
|
|
Paying out fictitious salaries
|
In addition to
claiming the proceeds of crime as legitimate business revenue, criminally-controlled companies also help legitimate certain participants in a criminal conspiracy by providing them with salaries. In some cases, salary checks were signed back to the company by the “employee” as part of the laundering operation. |
|
|
The significance of a trust account — whether onshore or offshore
— in the context of money laundering cannot be understated because: |
It
can be used as part of the first step in converting the dirty cash into less suspicious assets, it can help hide criminal ownership of funds or other assets, and it is often an essential link between different money laundering vehicles and techniques, such as real estate, shell and active companies, nominees and the deposit and transfer of criminal proceeds. |
|
|
“bearer shares,”
|
Bearer bonds and bearer stock certificates, or “bearer shares,”
are prime money laundering vehicles because they belong, on the surface, to the “bearer.” |
|
|
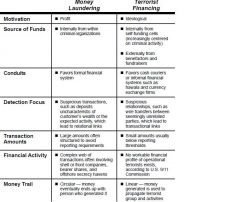
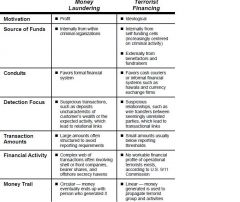
most BASIC difference b/n ML and terrorist financing
|
Terrorist
financing uses funds for an illegal political purpose, but the money itself is not necessarily derived illegally. |
|
|
|
|
|
9/11 Account Profiles:
|
Accounts were opened with cash/cash equivalents in
the average amount of $3,000 to $5,000 Identification used to open the accounts were visas issued through foreign governments Accounts were opened within 30 days after entry into the U.S. All accounts were normal checking accounts with debit cards The hijackers tended to open accounts in groups of three or four individuals |
|
|
additional 9/11 profiles
|
Some of the accounts were joint accounts
Addresses used usually were not permanent (i.e., mail boxes) and changed frequently The hijackers often used the same address/telephone numbers on the accounts No savings accounts or safe deposit boxes were opened The hijackers opened their accounts at branches of large, well-known banks Twelve hijackers opened accounts at the same bank |
|
|
9/11 Transaction profiles:
|
Some accounts directly received/sent wire transfers of
small amounts from/to foreign countries such as United Arab Emirates (UAE), Saudi Arabia, and Germany Hijackers made numerous attempts of cash withdrawals that often exceeded the limit of the debit card High percentage of withdrawals was from debit cards Low percentage of checks was written Numerous balance inquiries were made After a deposit was made, withdrawals occurred immediately There was no discernible pattern of timing of deposits/ Disbursements |
|
|
Additional 9/11 transactional activity:
|
Account transactions did not reflect normal living
expenses for rent, utilities, auto payments, insurance, etc. Funding for daily expenditures was not evident from transactions Overall transactions were below reporting requirements Funding of the accounts was by cash and overseas wire transfers ATM transactions occurred with more than one hijacker present (uninterrupted series of transactions involving several hijackers at the same ATM) Debit cards were used by hijackers who did not own the accounts |
|
|
9/11 International activity:
|
Three of the hijackers supplemented their financing
by opening foreign checking accounts and credit card accounts at banks located in the UAE While in the U.S., two of the hijackers had deposits made on their behalf by unknown individuals Hijackers on all four flights purchased traveler’s checks overseas and brought them into the U.S. These traveler’s checks were partially deposited into their U.S. checking accounts Three of the hijackers (pilots/leaders) continued to maintain bank accounts in Germany after moving to the U.S. |
|
|
Additional 9/11 International Activity:
|
Two of the hijackers (pilots/leaders) had credit cards
issued by German banks and maintained those cards after moving to the U.S. One of the hijackers (pilot/leader) received substantial funding through wire transfers into his German bank account in 1998 and 1999 from one individual In 1999, this same hijacker opened an account in UAE, giving power of attorney over the account to the same individual who had been wiring money to his German account More than $100,000 was wired from the UAE account of the hijacker to the German account of the same hijacker in a 15‑month period |
|
|
To
avoid becoming conduits for terrorist financing, institutions are told they can look at these examples and others that it provides: |
Use of an account as a front for a person with
suspected terrorist links revealed by a previous suspicious transaction report Appearance of an accountholder’s name on a list of suspected terrorists, such as that issued by the UN Security Council Committee on Afghanistan Companies that were subject to previous suspicious transaction reports and through which many funds transfers pass in a short time Frequent large cash deposits in accounts of non-profit organizations High account turnover in relation to accountholder’s salary Lack of clear relationship between banking activity and nature of accountholder’s business. |
|
|
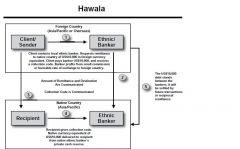
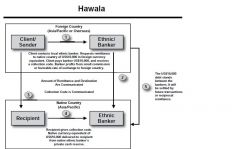
Hawala, hundi or so-called “underground banking”
|
are alternative
remittance systems or informal value transfer systems that are often associated with ethnic groups from Africa or Asia, and commonly involve the international transfer of value outside the legitimate banking system. They are based on trust. |
|
|
|
|
|
Hawalas are attractive to terrorist financiers because_____
|
they, unlike
formal financial institutions, are not subject to potential government oversight and do not keep detailed records in standard form. Although hawaladars do keep ledgers, their records are often written in idiosyncratic shorthand and maintained only briefly. |
|
|
Charities or non-profit organizations have characteristics that are
particularly vulnerable to misuse for terrorist financing. They (5 points): |
Enjoy the public trust
Have access to considerable sources of funds Are often cash-intensive. Often have a global presence, often exactly in or next to those areas that are most exposed to terrorist activity. Often are subject to little or no regulation or have few obstacles to their creation |
|
|
The FATF recommends that non-profit organizations to combat terrorist financing:
|
Maintain and be able to present full program budgets
that account for all expenses Conduct independent internal audits and external field audits, the latter to ensure funds are being used for intended purposes |

